Description
In this course, you will learn:
- How to tell if an attack is taking place inside a network.
- How to get proof of network intrusions.
- How to check for vulnerabilities in networks and systems.
- How to prepare for network assaults and protect against them.
Syllabus:
- Packet Sniffing
- Password Cracking
- Port Scanning
- Exploits and Exploiting
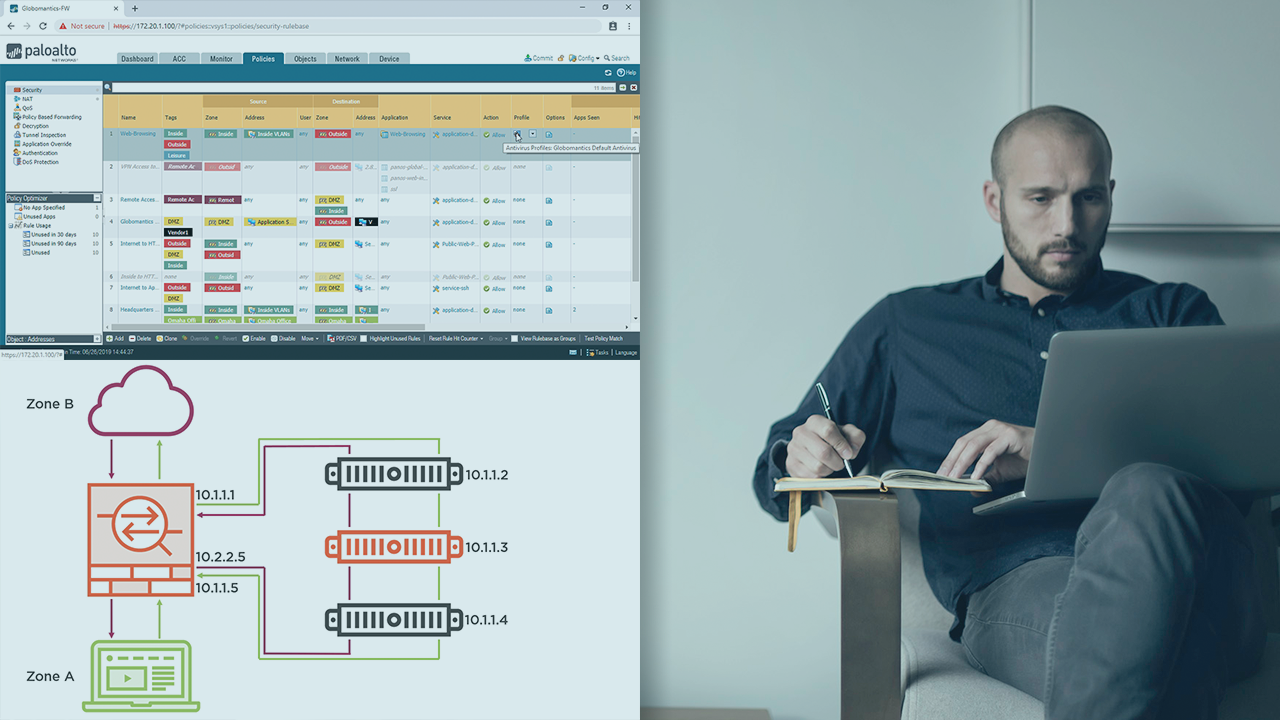
- Access Control Lists
- Snort
- DHCP, DNS, and Switch Attacks and Mitigations
- Man in The Middle Attacks and Mitigations