Description
In this course, you will :
- Learn how to set up a secure cloud environment on AWS.
- see an overview of fundamental AWS service offerings and how they relate to infrastructure security.
- Learn how to secure your cloud data and allow secure communication between cloud services.
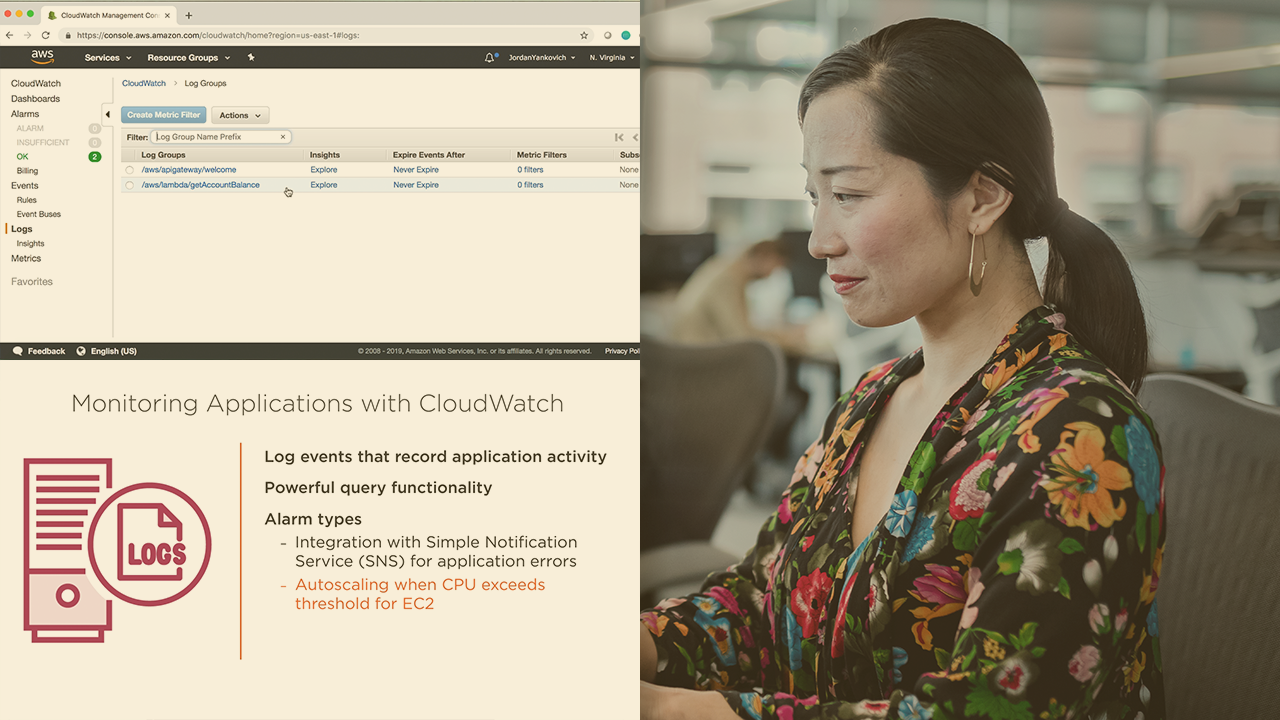
- Investigate how cutting-edge logging and monitoring solutions can help you maintain a secure enterprise cloud environment.
- After completing this course, you will have the AWS skills and knowledge required to create a secure cloud environment.
Syllabus :
1. Identifying AWS Services for Security and When to Use Them
- Contextualizing AWS Cloud Security
- Creating AWS Users with Identity and Access Management (IAM)
- Overview of Additional AWS Services Used for Security
- Enabling Secure Communication Between AWS Services
2. Define the Shared Responsibility Model
- Understanding the Shared Responsibility Model
- Securing Infrastructure Services
- Securing Container Services
- Securing Abstracted Services
3. New Module
- Maintaining a Secure Environment
- Managing Environment Authorization
- Logging Fundamentals in CloudWatch
- Searching through Service Logs
- Detecting Environment Vulnerabilities