Description
In this course, you will learn :
- With the USB forensics writeblocking and impersonation, you can learn USB forensics and penetration testing.
- In Linux, you can easily and cheaply investigate writeblocking USB mass storage devices.
- Make a low-cost USB pocket writeblocker.
- Learn how to create a USB impersonator capable of bypassing endpoint security software.
- By the end of this course, you'll know how to writeblock USB drives on your Linux forensics workstation as well as on the go with a small device.
Syllabus :
1. Software Write Blocking with Udev Rules
- Udev Rule Basics
- Creating Writeblocking Udev Rules
- Making It Easy with an Install Script
- Writeblocking Demonstration
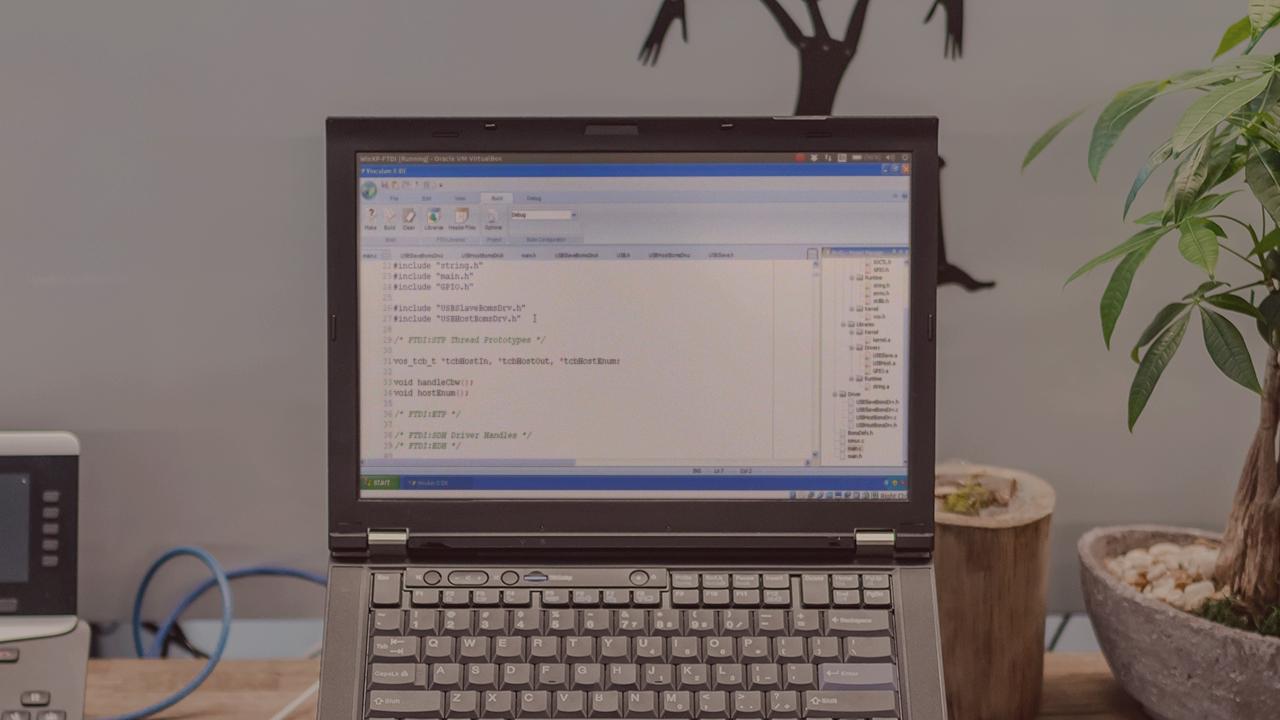
2. Hardware Write Blocker Based on VNC2
- Automatically Generated Code and Threads
- Helper and Handler Functions
- Miscellaneous Items and Device Programming
- Writeblocker Demo
3. USB Impersonation
- Introduction and Motivation
- Code Walk Through 6m
- Demonstration and Course Summary